Win32.Worm.Welchia.B exploits the vulnerabilities Buffer Overrun in RPC Interface, WebDAV and Workstation Service Buffer Overrun in order to spread to as many computers as possible.
Win32.Worm.Welchia.B spreads by attacking remote computers and exploits the vulnerabilities mentioned above to download a copy of itself to the compromised computer. In order to do this, Win32.Worm.Welchia.B incorporates its own web server.
Win32.Worm.Welchia.B uninstalls the worms Mydoom.A and Mydoom.B, by ending their processes and deleting the files carrying the worms.
Welchia in Registry
HKEY_LOCAL_MACHINE “\SYSTEM\CurrentControlSet\Services\” “RpcPatch”
HKEY_LOCAL_MACHINE “\SYSTEM\CurrentControlSet\Services\” “RpcTftpd”
Welchia in folder
C:\WINDOWS\SYSTEM32\wins\svchost.exe
C:\WINDOWS\SYSTEM32\wins\dllhost.exe
Know more about Welchia in Wikipedia
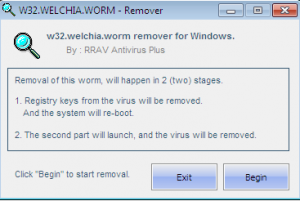
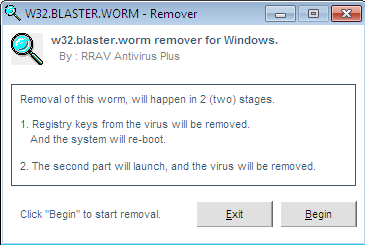
Screenshot:
 Download Now
Download Now